The Kronos banking malware family was first known to be sold in the underground market in 2014. It surfaced again in mid-2017 after being dormant for some time. Then, in

On September 19, 2018, Juniper Threat Labs discovered a new wave of attacks from a cryptominer worm targeting Linux servers, home networking devices, and IOT devices. These attacks were bundled

Co-Authors: Anoop Saldanha and Paul Kimayong Gozi, also known as Ursnif, is a well-known banking malware. Many variants of the malware family were identified in different attacks after its source

When first publicly announced on May 23, the threat dubbed VPNFilter was thought to only infect some brands of home routers and Network Attached Storage devices. While it was known

VPNfilter is a campaign to compromise small office and home routers as well as Network Attached Storage devices from several popular manufacturers. According to a Cisco Talos blog, there are

Nukebot (aka TinyNuke, or NuclearBot) made the news in spring of 2017 when the author released the source code in an attempt to restore their/his/her reputation in the cybercrime ….
Crypto ransomware seems to be a never-ending threat in today’s cyber world. It’s comparable to the “Kaiju” in the 2013 Hollywood blockbuster, Pacific Rim. One crypto ransomware dies and another
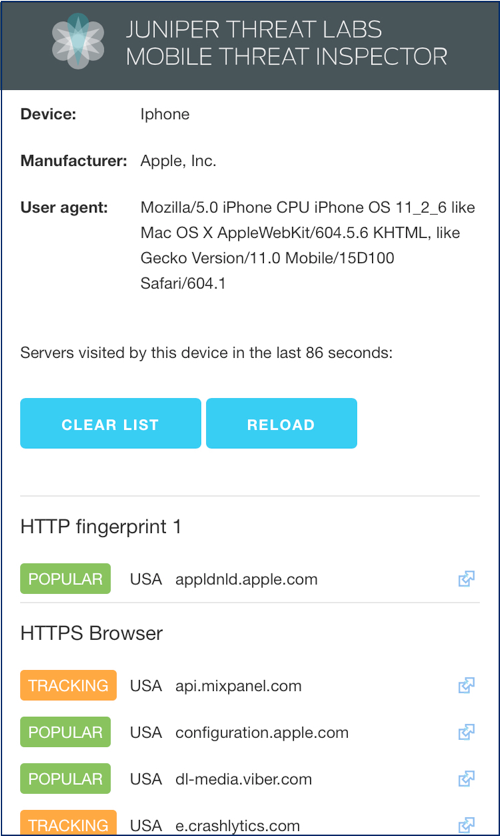
What is your phone up to? Your average enterprise security team requires access to all traffic in order to provide the secure environment that companies need to safely perform their
Threat name: BitPaymer Ransomware IOC Hash: Sha256: 8943356b0288b9463e96d6d0f4f24db068ea47617299071e6124028a8160db9c IOC Files: Files encrypted changed to extension .locked Files ending with Readme_txt are created containing the Ransom Notes BitPaymer ransomware was first

During the early weeks of February 2018, Juniper Threat Labs detected several malicious email campaigns involving a malicious MS Office file. The file attachment is an RTF file that includes























