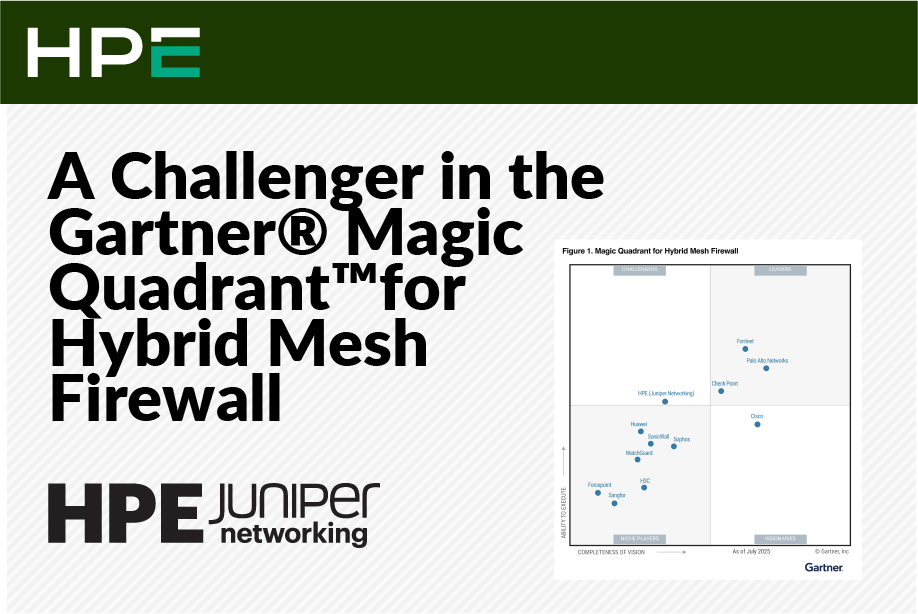
Why we believe HPE Juniper Networking’s position as a Challenger underscores the power of the secure AI-native networking platform. The evolving landscape of cybersecurity demands innovation—not only in technology, but

At Juniper Networks, we understand that delivering the highest levels of data and information confidentiality, integrity, and availability is paramount to earning and retaining our customers’ trust. That’s why we’re
Introduction As your organization embraces cloud-native technologies and Kubernetes, the complexity of securing your infrastructure grows exponentially. Traditional network security solutions often struggle to keep pace with the dynamic nature
The quantum computing era has officially arrived, which is a good thing. Quantum has the potential to advance our understanding of the world and make incredibly complex decisions faster than

In our ever-connected world, security efficacy has become more than just a buzzword phrase—it’s now a critical necessity for organizations everywhere. As cyber threats grow increasingly sophisticated, ensuring robust security

In today’s dynamic digital landscape, security has evolved from a technical necessity into a baseline requirement for building trust and maintaining agility in the marketplace. It’s why IT and business
On August 1, 2024, Retail payments began to be disrupted in Indian banks and suddenly, massive news broke, stating Brontoo Technology Solutions – a collaborator with C-Edge Technologies, which is
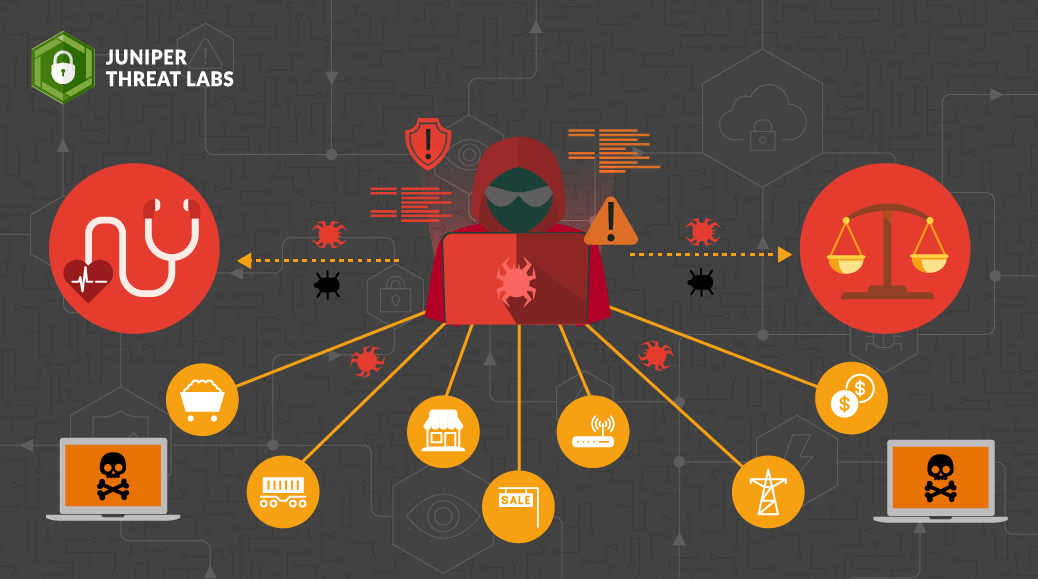
Since its emergence in 2022, the BianLian ransomware group has rapidly evolved, showcasing sophisticated techniques and adapting to the shifting landscape of cyber threats. It’s among the top three most

For the last 20 years, networking and security teams have had quite a tumultuous relationship thanks to vastly different objectives and/or impact on the other when completing necessary tasks. Security

Let’s face it, organizations often struggle to address unwanted behaviors on the network while minimizing their potential impact. Ideally, incidents would be addressed in real-time with automated responses to prevent