PaperCut is an enterprise print management software. PaperCut NG is used for managing and controlling printing. PaperCut MF is a more advanced solution that, in addition to managing printing, can
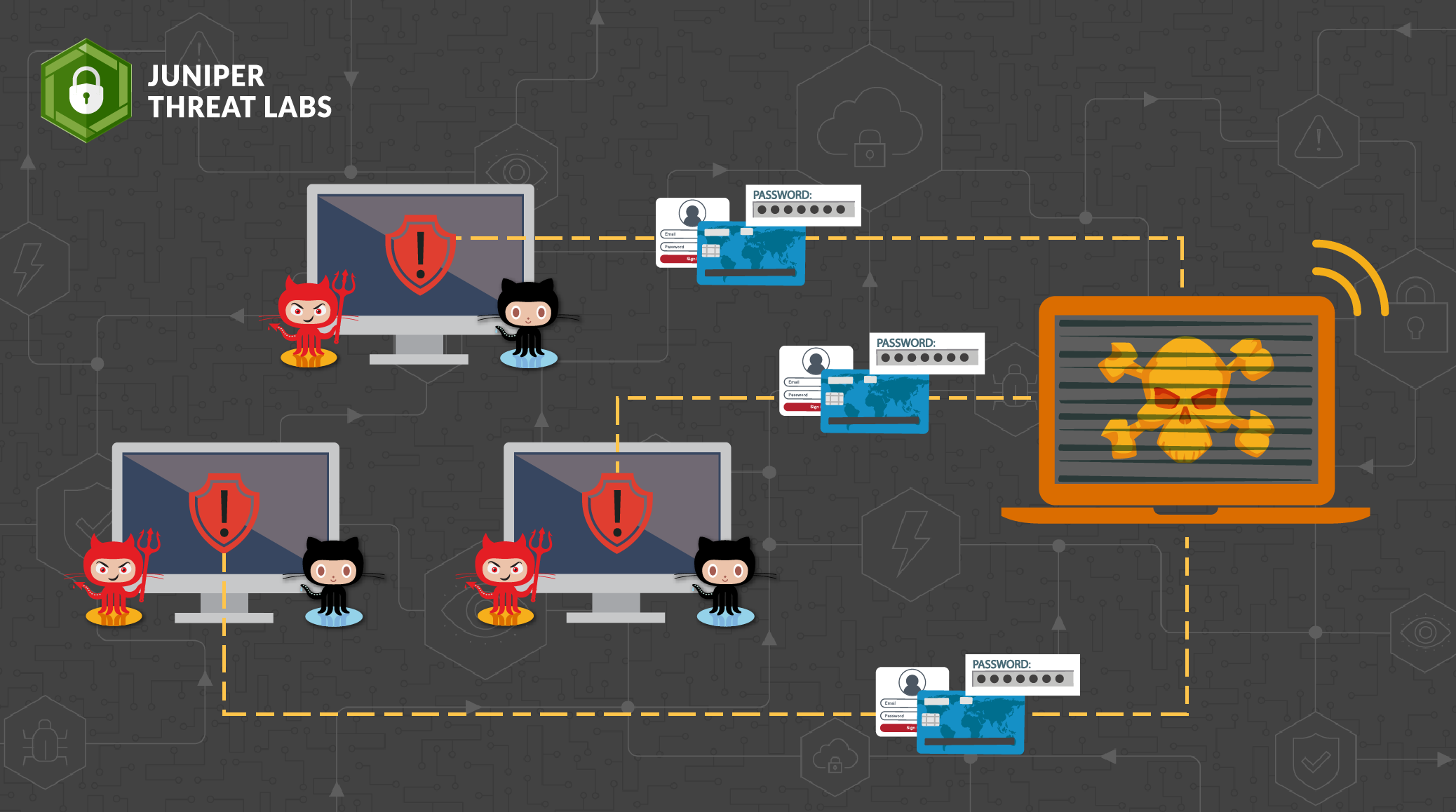
GitLab is a web-based platform for version control, CI/CD pipelines and collaboration on software development projects. An arbitrary path traversal vulnerability has been recently reported in the GitLab Community Edition
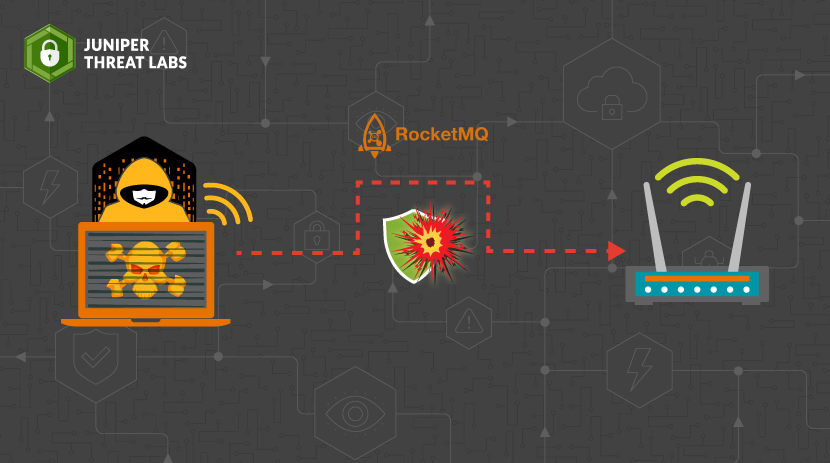
Apache RocketMQ is one of the most popular and widely used distributed messaging and streaming platforms. A command execution vulnerability has been recently reported in Apache RocketMQ affecting version 5.1.0

The capabilities of OpenAI’s large language model have astounded, delighted and (at times) horrified those who have tried it. Much ink has been spilled speculating which professions will be replaced
Email is an essential service for companies and individuals. Billions of emails are exchanged daily, and within a portion of those emails lurk malware aimed at compromising your organization’s network
In October 2022, Juniper Threat Labs discovered a backdoor implanted on a VMware ESXi virtualization server. Since 2019, unpatched ESXi servers have been targets of ongoing in-the-wild attacks based on

Introduction Juniper Threat Labs is currently monitoring an emerging Chinese Remote Desktop Trojan called Asbit. It’s a remote access Trojan being advertised on its developer’s website as a “Fast
A zero-day vulnerability was discovered on Microsoft Windows Support Diagnostic Tool (MSDT). On May 27, a researcher who goes by the twitter handle nao_sec discovered an interesting Microsoft Word document

Juniper Threat Labs has uncovered an attack that targets Redis Servers using a recently disclosed vulnerability, namely CVE-2022-0543. This vulnerability exists in some Redis Debian packages. The attack started on
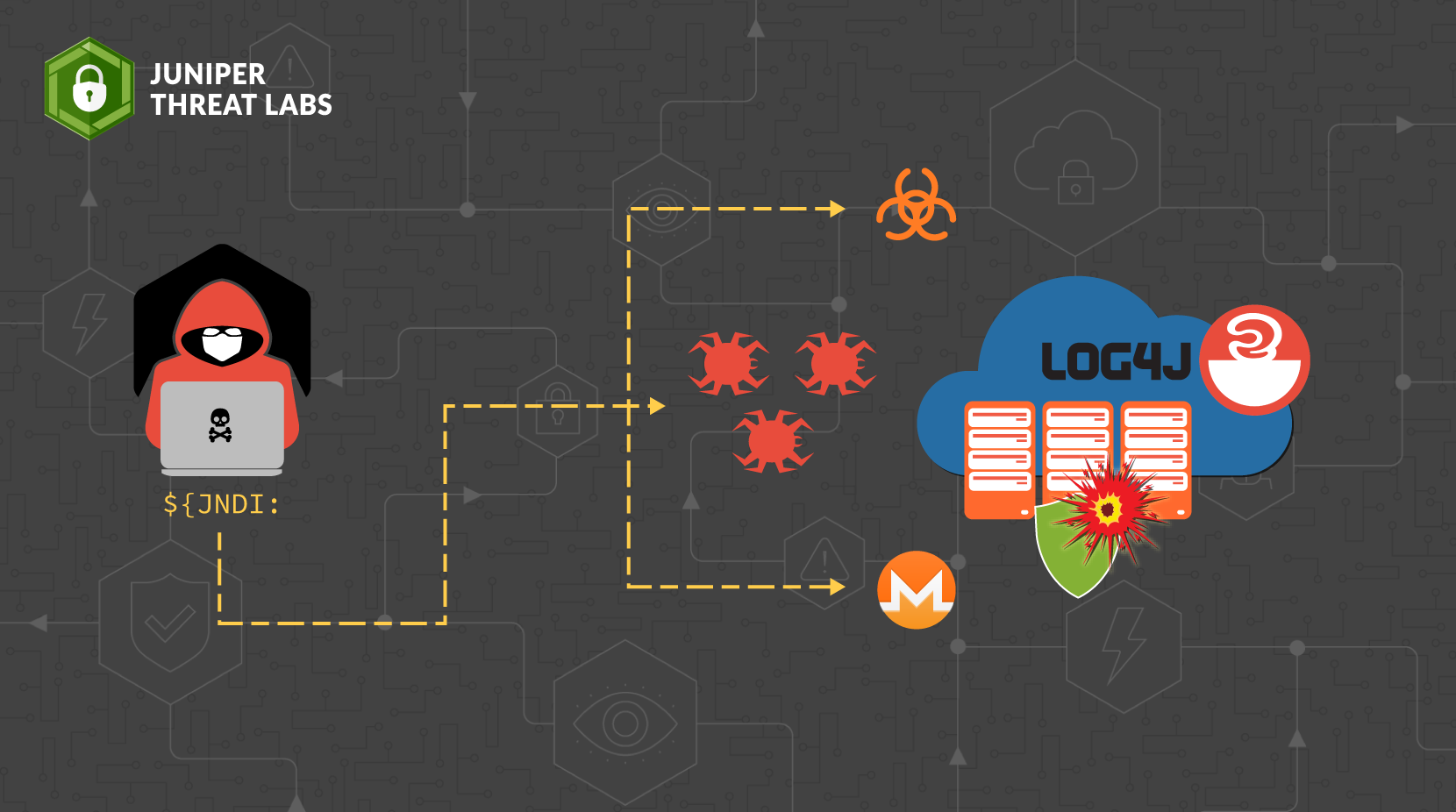
Juniper Threat Labs compiled a list of the payloads from log4j attacks we have seen as of 12/16. Most of the payloads install malware such as Muhstik, Kinsing, Mirai and






















