When network access control (NAC) debuted in the early 2000s, its purpose was relatively straightforward: provide secure access by authenticating and authorizing corporate computers and laptops on a company’s private network. Over the years, that list of connected devices grew exponentially with the addition of BYOD, guest access and IoT devices. To address this growth, on-premises NAC platforms bolted on new features and functions that required more horsepower from the hardware and more complicated configurations and oversight to manage. As a result, the world of networking has ended up with complex NAC solutions that lack the global scalability and flexibility to securely connect users with their applications and data from any device.
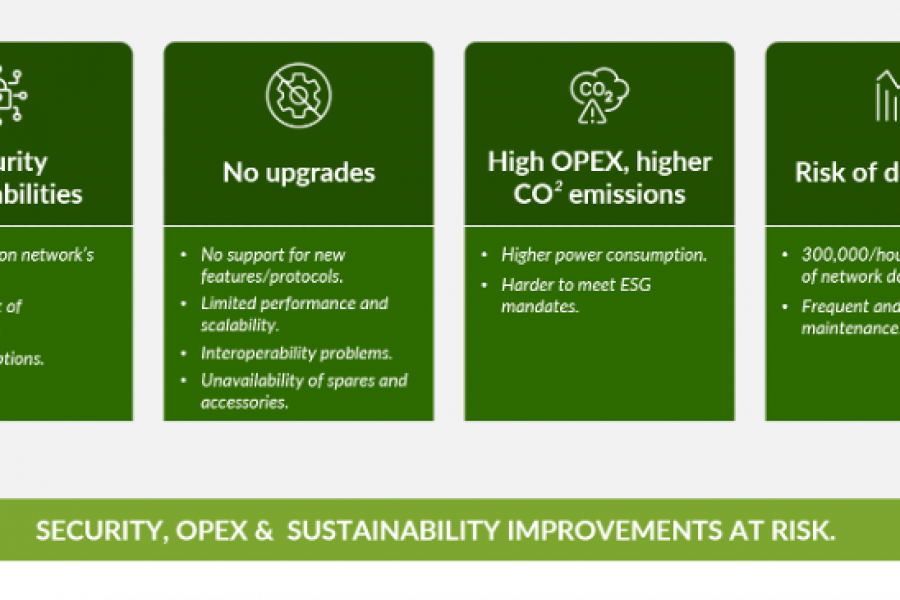
Today’s NAC solutions present several challenges:
- They are 20-year-old brittle and complex platforms with monolithic code
- They are cumbersome to troubleshoot
- Their design does not incorporate user experience insights
- They lack the agility and scale needed for today’s growing networks
- Their maintenance, feature updates and security patches require downtime and technical expertise
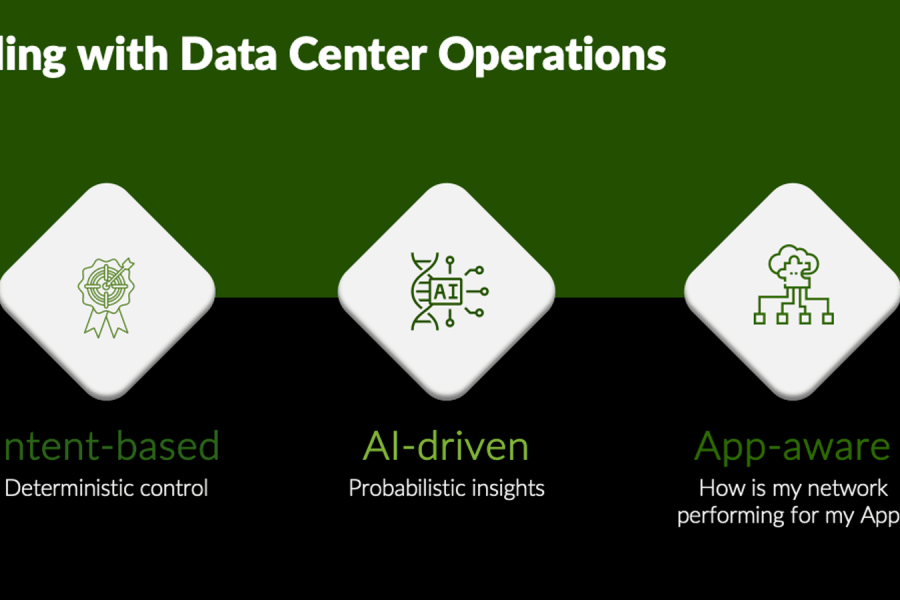
While NAC has remained stuck in the past and on-premises, the rest of the network architecture has moved on to the cloud. Juniper’s Mist AI architecture exemplifies simpler network operations with AI-driven automation and insight, coupled with the agility and reliability of a microservices cloud to deliver optimized user experiences. This allows IT teams to streamline operations and make user and device troubleshooting painless, while empowering teams to deliver innovative and strategic solutions that support new business objectives.
Moreover, with network operations moving to the cloud, so have identity provider services (IdPs). IdPs moved to centralized identity management for several reasons, including cloud security, scalability and reliability, enabling remote identity processes and reducing cost with no software and hardware to purchase and manage.
So, what’s the next stage for NAC? It’s time to get rid of legacy solutions’ software and hardware headaches and utilize the power of a true microservices-based cloud.
Enter the Modern Cloud for NAC: Juniper Mist Access Assurance
Juniper is proud to announce a paradigm shift in network access control (NAC) with the latest expansion of our Juniper Mist AI-driven enterprise portfolio, Juniper Mist Access Assurance! Access Assurance is our cloud-based NAC service that enables enterprises to easily enforce secure network authentication and authorization without the challenges associated with on-premises NAC.
Getting rid of on-premises NAC provides a streamlined client-to-cloud user experience, inherent high-availability services and greater resilience, as well as automatic feature updates and bug fixes. It’s simple, secure and scalable with no downtime for upgrades and tackles the complexity and poor scalability of legacy solutions such as Aruba ClearPass and Cisco ISE.
Access Assurance was born from Juniper’s 2022 acquisition of WiteSand and its cloud-native NAC technology experience. We integrated WiteSand technology with our AI-driven Juniper Mist cloud service to provide users a full suite of access control functionality with a flexible, simple authorization policy framework for onboarding guest, IoT, BYOD and corporate devices.
Full-Stack Integration for Simplified Operations
From the start, Access Assurance was designed to enable a secure and reliable user connection experience on the network. By integrating NAC with network connection visibility, we continuously validate the end-user experience, pinpointing issues whether they’re caused by client configuration, network services or NAC policies. All client events are captured by the Juniper Mist cloud, simplifying day-to-day operations and quickly identifying end-user issues.
A single pane of glass offers end-to-end visibility for all parts of the network driven by Mist AI. Access control is not a bolt-on feature; it’s purposefully built into the Juniper Mist cloud to provide scalability and simplicity that complements the full-stack management and day-to-day operations of an enterprise’s Wi-Fi access points, wired switches and SD-WAN. The Marvis™ AI engine also leverages access data for anomaly detection to provide actionable metrics.
Cloud-Native Platform
The Juniper Mist microservices-based cloud architecture keeps Access Assurance optimized with the most advanced technologies. New features, security patches and updates are automatically added without interruptions or service downtime just like the rest of Juniper’s Mist cloud services. This capability dramatically simplifies and improves service operations for network IT administrators by eliminating lengthy software upgrades and service downtime. There’s no more worrying about glitchy software upgrades, hardware/VM issues or delayed updates on the system. Juniper eliminates all that grief.
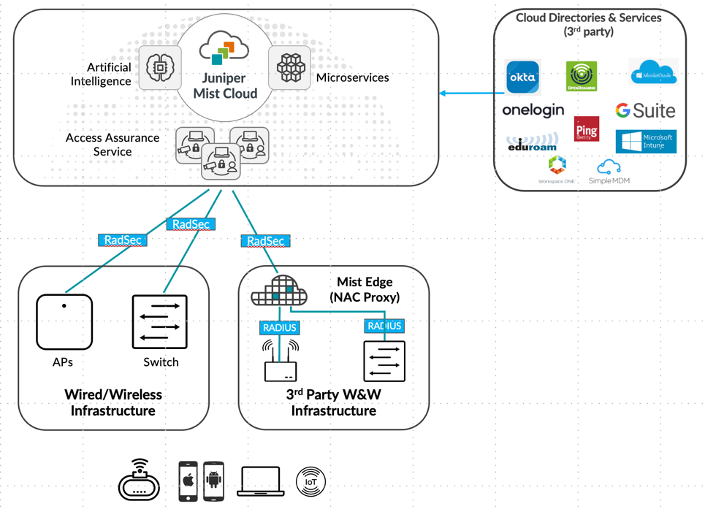
Figure 1. The Juniper Mist Cloud with Access Assurance Service
With Access Assurance, organizations also gain reliable, secure, low-latency NAC, whether they need to cover a single location or multi-site deployments. Secure communication between the Access Assurance cloud, on-site switches and access points is via RadSec. Juniper has also deployed cloud instances of Access Assurance in multiple regional locations to direct authentication traffic to the nearest instance for optimal response time and low latency.
Network Policy Enforcement
One of the most important facets of Access Assurance is the simplicity of its network policy creation and enforcement. Based on user and device identity, Access Assurance instructs the network to assign users specific roles and group them into network segments using VLAN or Group-Based Policy (GBP) technology. The service can then enforce network policies associated with each segment. With Access Assurance, creating and applying policies takes minutes – unlike on-premises solutions where this process can take hours bouncing around inside various configurators.
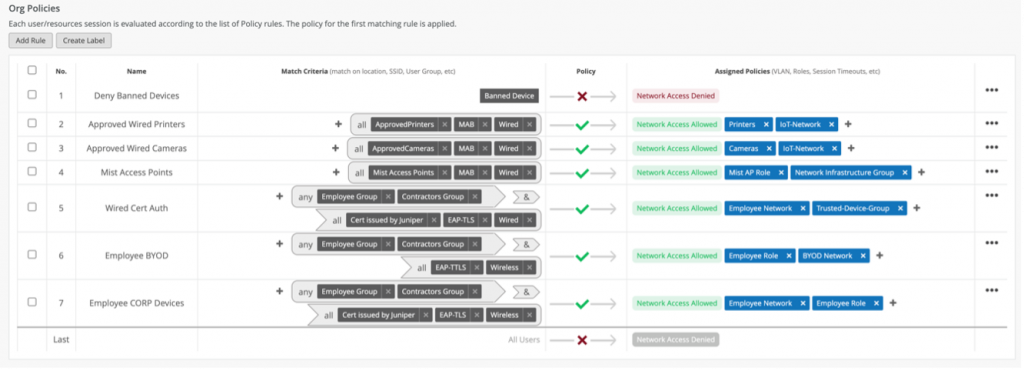
Figure 2. The flexible policy creation interface helps admins assign policies based on business requirements.
External Identity and Directory Services Support
Access Assurance provides authentication services by integrating external directory services, such as Google Workspace, Microsoft Azure Active Directory, Okta Workforce Identity, etc. It also integrates external Public Key Infrastructure (PKI) and MDM platforms.
And since the Juniper Mist platform is 100% programmable using open APIs, it enables easy integration with any IdPs and security information and event management (SIEM), IT service management and other platforms for both configuration and policy assignment.
What Does it All Mean?
NAC has turned into quite an unpleasant (but necessary) evil over the years due to its convoluted history and current state of existence. Juniper has taken a clean sheet of paper to redesign NAC for the cloud era, making it simple and straightforward to use, while still providing the optimal protection for devices and users accessing the network. Now, network administrators have a near-effortless way to manage access and deliver a better user experience via a common cloud and AI engine.
Unlock the most powerful, cloud-native, AI-driven Access Assurance service available today. Now, NAC is back and better than ever with Juniper Networks!
Learn more:
- Read the Press Release
- Visit the Juniper Mist Access Assurance product page
Additional Resources:
Webinar: 5 Steps to Simplify and Secure your Network
Juniper Mist IoT Assurance
Juniper Mist Wi-Fi Assurance
Juniper Mist Wired Assurance
Enabling the AI-Driven Enterprise
Access Assurance Video
Marvis, the Virtual Network Assistant (VNA), Now Integrates With ChatGPT
Marvis Learns About Zoom User Experiences to Improve Network Performance
Statement of Product Direction
Juniper Networks may disclose information related to development and plans for future products, features or enhancements, known as a Plan of Record (“POR”). These details provided are based on Juniper’s current development efforts and plans. These development efforts and plans are subject to change at Juniper’s sole discretion, without notice. Except as may be set forth in definitive agreements, Juniper Networks provides no assurances and assumes no responsibility to introduce products, features or enhancements described in this presentation. Purchasing decisions by third-parties should not be based on this POR and no purchases are contingent upon Juniper Networks delivering any feature or functionality depicted in this presentation.