Information security must be about far more than simple prevention. Preventing cyberattacks is a critical component of modern information security, however, on its own prevention is inadequate. Understanding dwell time is useful in understanding why.
The Inevitability of Compromise
At some point, your network will be compromised. Regardless of how great your perimeter network defenses are, or who makes them, compromise is inevitable.
To successfully defend against all attacks, defenders must be capable of defending against every possible type. They must defend against bad guys attacking from across the internet., malicious insiders, human error, technological failure, mechanical breakdown, well intentioned people pushing the wrong button and entirely random incidents like “someone backed a cement truck through the wall of the data center”. (True story; happened to me.)
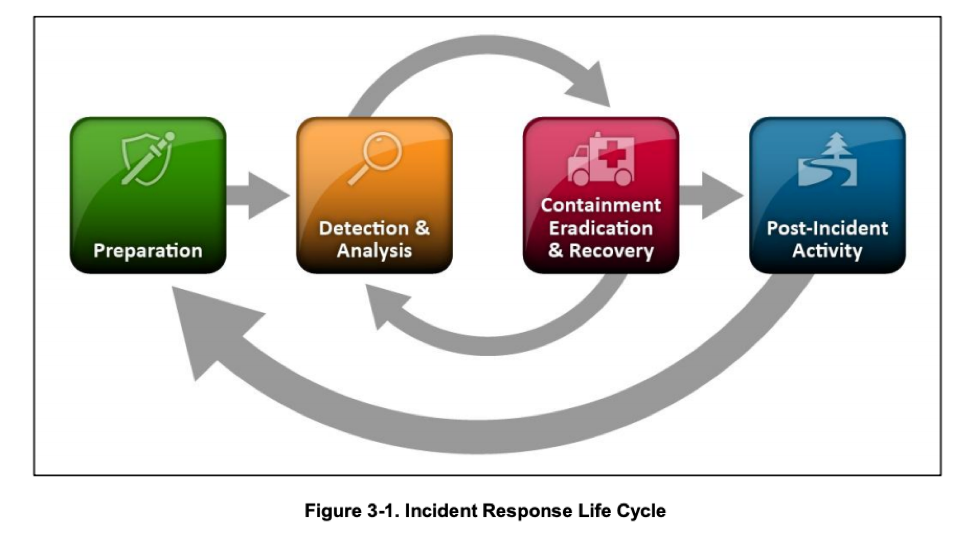
Success in information security requires planning for the inevitable compromise. This requires detecting that a compromise event has occurred, reacting to the issue, restoring services to normal activity and then dealing with the aftermath.
Any network compromise poses the risk of lateral movement. This is industry jargon for “once the bad guys have breaches into your network, they can use that as an entry point to attack the rest of your network”. Lateral attacks are frequently successful because most organizations rely almost exclusively on perimeter defenses; once behind the edge firewall, the network is wide open.
Planning for the inevitability of compromise has two components: mitigation and incident response.
Mitigation
The current industry best practices approach to mitigating the effects of inevitable compromise is to put additional defenses in place to prevent lateral spread. Without getting in too much detail, the most effective approaches basically involve sprinkling firewalls all over the network.
It has been standard industry advice for each workload to have its own firewall for decades. These help but aren’t enough. Microsegmentation – breaking up networks using VLANs and VXLANs – is another important tool.
Administrators properly applying microsegmentation will wrap up each individual application in its own network segment. This way, the multiple workloads that make up an application are able to talk to one another freely but can’t communicate outside of their own microsegment without passing through a router.
That router becomes a potential point of inspection, much like the edge defenses organizations put between their networks and the internet. Intrusion detection, advanced threat protection, monitoring and more can all analyze traffic passing between microsegments.
As a means of mitigating compromise, microsegmentation and Network Functions Virtualization (NFV) are among our most powerful tools…but getting there is often a long journey. It is great to have a goal but organizations need to defend what they have today, and very few have full scale microsegmentation in place.
Automated Incident Response
If you can’t limit the lateral spread of compromise using microsegmentation and NFV, the concept of dwell time must become your focus. Dwell time is the amount of time that passes between when a compromise event begins and when it has been contained.
The job of the defender is to architect their networks such that compromise events have the shortest possible dwell time.
If it takes 5 minutes to detect a compromise and 15 minutes to contain it, then the dwell time for that compromise event is 20 minutes. Defenders must reduce both time to detection and time to containment in order to be successful; this is where having the right information security technologies in place makes all the difference.
Better detection technologies reduce time to detection. Reducing time to containment, however, is all about what you do once the compromise event has taken place.
Here, automation is key. If a defender’s information security systems can detect a compromise event, then with the right technologies and a little bit of work that detection can be used to trigger automatic containment of compromised hosts, workloads and/or infrastructure components.
With Juniper Connected Security, defenders can leverage event driven security to automatically isolate hosts, workloads and/or infrastructure components in order to quarantine compromised areas of the network. Juniper Connected Security can automate incident response from an individual user’s endpoint, to cloud and all points in between; including on third party infrastructure!
The ability to isolate hosts at the switch port (or wireless access point) level is a critical capability for rapid containment and reducing the dwell time of threats. It will be years before most organizations are able to build fully microsegmented networks, and many organizations may never invest fully in NFV to defend each of their network segments. Automated incident response allows us to not only to defend the networks of today, but also buys time to adapt to the evolving role of the network perimeter and the harsh reality of inevitable compromise.
Juniper Connected Security
Juniper Connected Security provides enterprises with the tools they need to protect their networks. We offer industry-leading perimeter defenses to minimize the number of compromise events that occur. We have monitoring and detection capabilities to identify issues when they occur. We have automation and policy enforcement platforms to automatically contain threats, in addition to the one of the most flexible microsegmentation offering currently available.
Most importantly, Juniper Connected Security connects and automates more than just Juniper’s own products. No vendor, no matter how capable, can defend a modern enterprise entirely with their own products. Attackers will use all the tools at their disposal and defenders must have the ability to do the same.
This – defense in depth – is the core concept behind Juniper Connected Security. Multiple layers of defenses, from multiple vendors, all working – and automated – together.
To learn more, please view our automation webinar series as we take a look at the next stage of the security automation journey.