Welcome to the Juniper #RSAC2020 liveblog! Stick with us for live updates on the hottest topics being discussed throughout the conference. We are excited to hear what’s on the minds of conference attendees, specifically what their top real-world security concerns are as we enter a new decade.
If you are attending #RSAC 2020, stop by and say hi, and let us know what you think. We’re in the North Hall, Booth #6161.
Ransomware: The Evolving Threat
Ransomware is still a hot topic in 2020! Last year, we saw ransomware evolve from a simple threat which encrypts data and holds it for ransom, into a threat which exfiltrates data and threatens to leak it unless the ransom is paid. So far, we are hearing a lot about concerns around ransomware throughout the conference.
Fortunately, Encrypted Traffic Analysis (ETA) can help! ETA is a new tool in our battle against malware which allows IT teams to analyze encrypted data flows to determine their threat level, using a machine learning based analysis of the encrypted session setup and certificate exchange.
Keeping It Real with Big Data
For most of the last 15 years, the IT industry has relentlessly pushed the Big Data narrative: there’s gold in them thar data centers. If only we could aggregate enough data, and find the right algorithms to massage that data for those golden insights. While this data can prove beneficial, it is a double-edged sword as data still carries risk. Data warehouses and data lakes are jackpots for threat actors, and organizations need to understand the liability data can pose.
Protecting against the risks posed by data aggregation is easiest when organizations have deep network visibility and the ability to enforce policy at every point of connection throughout the network. Detecting data exfiltration attempts as early as possible are key to managing the risks posed by retaining data.
Social Media + Machine Learning: A Perfect Storm?
You can’t go anywhere in 2020 without hearing about how social media has evolved, and how based on your social media interactions, data can be gathered on you and everyone you’re connected with (and that they are connected with). Now complicating matters, is the rise of machine learning, which is getting better at extracting information and context from social media streams.
It’s almost too easy – for example, by simply follow all of a company’s employees that you can find and start mining the accounts for information slips. In aggregate (and especially when arranged chronologically), this information can be compared to other data sources (such as SEC filings, Glassdoor reviews, LinkedIn profile changes, and more) to gain additional insight into an organization.
With this public information being widely available, it is easy for bad actors to strike. Disinformation can be spread to disrupt targets by encouraging them to implement standards other than best practices. This can be done by creating a veneer of legitimacy or consensus around questionable practices or standards. There is some concern about standards track corruption in this manner that is related to the elliptic curve concerns that has been a hot topic for the past few years and we see no sign of interest in this topic slowing down.
Risky Business: SOCs, Risk Management, Prioritization, and Categorization
Security Operations Centers (SOCs) are busy places. SOC teams regularly feel overwhelmed, and when things go wrong, they seem to go wrong all at once. How do organizations prioritize incidents in order to maximize the incident response effectiveness? How should they? How should security teams prioritize risks within an organization when they aren’t being actively exploited?
The evolution of security tools – from management suites to SIEMs – is one of the hot topics around risk categorization. How much can be automated? How much simply requires human review? What role does machine learning play, especially when we think about it in the context of real-time advanced threat protection? Regardless of the approach taken, deep network visibility is key.
Getting to the Root of It: The Debate Over Root Cause Analysis
One of the hot topics of debate here at #RSAC 2020 is root cause analysis. On one side, we have organizations who willingly publish a root cause analysis of widespread, well-reported outages. These analyses provide customer assurance and provide key learnings for other organizations to learn from.
On the other hand, there are many organizations that only perform a cursory root cause analysis or don’t invest in it at all. Of the organizations that perform root cause analyses, it is rare that outage analysis is shared publicly, and virtually no organizations report on their compromising events.
Why are there so many organizations not taking advantage of this vital tool? Should more information be publicly available, so that we can all learn from one another? Or do the individual risks to an organization outweigh the collective benefits?
There are several impassioned advocates for the differing views on this topic, but one consensus has emerged: the value of root cause analysis is greatly diminished if there is inadequate event data. It is necessary to detonate malware in sandboxes, explore kill chains, and review logs of data flows throughout the network – not just at the perimeter – and all are being discussed as important to root cause analysis.
Storm Warning: When Public Clouds are Attacked
At #RSAC2020, we are hearing concerns about the use of public cloud computing by attackers. Public cloud computing gives attackers the ability to easily scale everything from command and control infrastructure to decryption attempts, but it is the exfiltration of data that seems to be on everyone’s mind.
When data is exfiltrated, it must pass through an organization’s LAN, where possibly someone might notice a big spike in WAN data usage, especially if it takes a long time to steal the data. Attackers are using public cloud resources to attack an organization’s public cloud assets and can often exfiltrate large volumes of data very quickly, meaning that organizations cannot rely on noticing changes in WAN data volumes to detect the data exfiltration.
Shutting down these attempts before they ever reach the perimeter of a network is best, whether that network is on-premises or a virtual network located in a public cloud. The importance of deep network visibility, traffic inspection, and active threat analysis beyond the network’s edge are all reinforced during these discussions.
Keeping an Eye Out: The Concern over Surveillance
Surveillance is always a hot topic at any information security conference, and #RSAC2020 is no exception! Facial recognition is a hot topic again in 2020 and the discussion is expanding beyond its use by government and law enforcement agencies.
The positive and negative commercial implications of facial recognition are being fiercely debated in sessions, at vendor booths, as well as the hallways and lounges throughout the event. There is rising concern over citizen surveillance, which has been made far more prevalent thanks to user-friendly services like Amazon’s Ring. While the market isn’t currently saturated with solutions, that won’t always be the case, as technology improves it should be picked up by consumers in the way Amazon’s Alexa and Google Home have been embraced in households across the country. Much like the rise of social media and the ability to create profiles for people using big data, there is fear that surveillance could be added to that profile. We are seeing many parallels between this discussion and that of data being a liability, not an asset.
Networking and Talking InfoSec Careers at RSA
Careers are always a hot topic at conventions, as IT professionals from all stages of their career meet, discuss, and network. The value of mentoring has been repeatedly raised, and is often discussed in the context of an increasing number of people looking to retire from information security. Burnout, along with the loss of tribal knowledge about legacy applications and systems are serious concerns for many organizations.
Career paths into security, especially unusual ones, are another point of debate. Over the past year a number of individuals with non-tech backgrounds have become prominent within the information security community, and this has caused many to think about diversity of thought and experience. Inevitably, the value of certifications and whether those certifications are necessary have become part of the conversation.
Is a rich technical background a necessity to be an information security professional? Or is it enough to have an attitude of always looking for the exploit, and learn as you go? The debate will not be settled here, but so far everyone agrees that there is value in considering post-security career paths – even if only to remind us of why we love infosec! – as well as the clear benefits of disconnecting once in a while.
The Current State of Malware
It wouldn’t be a security conference without a lot of speculation about the evolution of malware! As a key tool for advanced threat actors, multi-vector malware has caused problems for the industry. Now, we are seeing spikes in malware families using multiple attack vectors. This increase in attacks against cloud infrastructure by on-premises malware has been noted in the industry. This type of malware that observes on-premises network traffic in order to obtain public cloud credentials, and then accesses those accounts from within an organization’s own on-premises network. Attacks against the public cloud infrastructure then look like they are occurring from within an organization’s own network, bypassing many traditional risk management approaches – such as limiting cloud administrative access to authorized IPs.
A “dropper” is a component of modern malware which allows attackers to download and install additional malware components. One concern being discussed is “fileless multi-dropper” malware. Fileless malware operates entirely out of RAM, and leaves no file footprint to detect. The use of multiple, narrowly tailored droppers to bypass defenses against different types of fileless malware, or to make use of multiple user contexts is a topic attracting much speculation.
The rise of ancient malware is another major topic today. Attackers seem to have realized that some security vendors retire malware signatures for malware strains that haven’t been seen circulating widely for some time, and this is leading to a resurgence in the use of some older families. Systems running unpatched and/or end-of-support operating systems, applications, or security defenses would be particularly vulnerable to this approach. This entire topic of discussion reinforces the importance of choosing information security products which do not retire signatures.
Malware hiding in subsystems has caused some animated conversations today! Many defenders feel powerless against this threat. Vendors frequently cease support for older subsystems, are lax about patching or may not be able to resolve a vulnerability at all. For these systems, the best place to catch malware is before it gets to devices in the first place, which demonstrates the importance of building threat aware networks that actively participate in their own defense.
As the capabilities of defenders improve, so to do those of attackers. Malware using nested tunnels (multi-tunnel malware) is rising in popularity. The use of HTTP over DNS over HTTPS is one example that has come up multiple times. One popular question is “how many tunnels can really be nested before the throughput becomes unusably slow?” Nested tunnels pose a real detection challenge, increasing the importance of both automated baselining and reputation-based threat analysis.
The Key to KMIPin Information Security
Key management is an important part of information security, and it is receiving an awareness boost at #RSAC2020 thanks to multi-vendor efforts to promote the Key Management Interoperability Protocol (KMIP). KMIP is a standard advanced by the OASIS standards body which defines message formats for the exchange of cryptographic information, opening the door to interoperability between key management products.
Securing all the Things
A quick journey to the expo floor will reveal vendors selling all manner of Internet of Things (IoT) gateways, smart devices, and more, but concern about the digitization of physical security is noticeable at #RSAC2020. Many vendors – including Juniper Networks! – have solutions to IoT security concerns which operate at the network layer, but recent successful attacks against IoT physical security devices have IT teams looking for ways to identify rogue IoT physical security devices installed without permission.
With “Shadow IoT” concerns now extending to physical access devices, there has been a lot of interest in vendors offering the ability to localize IoT devices. Juniper Networks’ Mist WI-Fi access points can help IT teams detect rogue Wi-Fi and Bluetooth devices, empowering existing Mist customers to counter this emerging threat.
Discussing Solutions to Attack Simulation
Chaos engineering, a discipline familiar to technologists thanks to the infamous Netflix Chaos Monkey, is being embraced by infosec practitioners at #RSAC2020. Attack simulation is approaching buzzword status as multiple vendors bring richly featured, viable products to market this year.
Attack simulation discussions are now shifting to practical concerns. What changes should organizations make to their network security models before engaging in attack simulation? How can data from attack simulation runs best be incorporated into existing development and operations practices? How can attack simulation be automated, and if vulnerabilities are discovered, how can mitigation be automated?
Threat-aware networks are a logical answer to these problems. Threat-aware networks actively participate in their own defense, offering deep network visibility, and the ability to enforce policy at every point of connection throughout the network.
This combination of visibility and enforcement mean that a threat-aware network can integrate with attack simulation efforts in order to limit the scope of impact to only what is intended. Threat-aware networks would also offer the ability to react in real-time to discovered vulnerabilities. Once again, Juniper Connected Security customers are prepared not only for the challenges of today, but building an infrastructure adaptable enough to handle tomorrow.
How Current Events are being Affected by Out-of-Band Access
Out-of-band access is the the ability to remotely administer a device through a channel different from the one used by that device to serve its primary role, is a popular feature. Unfortunately, out-of-band access is also rather infamous for being a frequently-ignored security vulnerability.
The announcement of a novel Intel Management Engine vulnerability only a few days before #RSAC2020 has raised the profile of this risk type at the conference. Fortunately, organizations can provide secure out-of-band access with Juniper Connected Security. Physical SRX-series firewalls, as well as NFX Network Services Platform appliances can be equipped with multiple methods of access while still offering a diversity of information security capabilities to secure networks of any scale.
NIST Secure Software Development Framework: The New Paper at RSA 2020
When the National Institute of Standards and Technology speaks, the IT industry listens. The NIST Secure Software Development Framework (SSDF) was discussed today, and it is expected to be an important document for developers throughout the industry, but especially any who intend to write code that will be used by the US federal government, or in regulated industries.
The SSDF is not an attempt to teach developers to write code without vulnerabilities. Instead, the SSDF exists to help developers adopt best practices which will mitigate the impact of the inevitable vulnerabilities that occur in all code. The draft paper has already generated plenty of discussion in the months leading up to #RSAC2020, something that looks set to continue throughout the rest of 2020.
Check out the draft of the paper here!
That’s a wrap on RSA 2020 – see you next year!
Thank you for joining us for our RSA recap, we learned a lot at RSA and we hope you did too! As the first major information security conference of the year, #RSAC2020 USA was an event with a lot of talk about the future…and reflection upon the past. Numbers and statistics were part of various sessions and keynotes, and we keep noticing the same trends this year as we have in years post: the scope and scale of attacks are increasing while attackers are becoming more and more sophisticated.
While it might be easy to see only doom and gloom amidst the constant reminders of increasing attacker capability, there is plenty of reason for hope. Data science researchers are learning how to identify which patches are statistically effective, allowing for more efficient prioritization. Machine learning and artificial intelligence are being increasingly incorporated into information security defenses and intelligence sharing regrading novel malware is having a helping to limit new malware outbreaks before they spread.
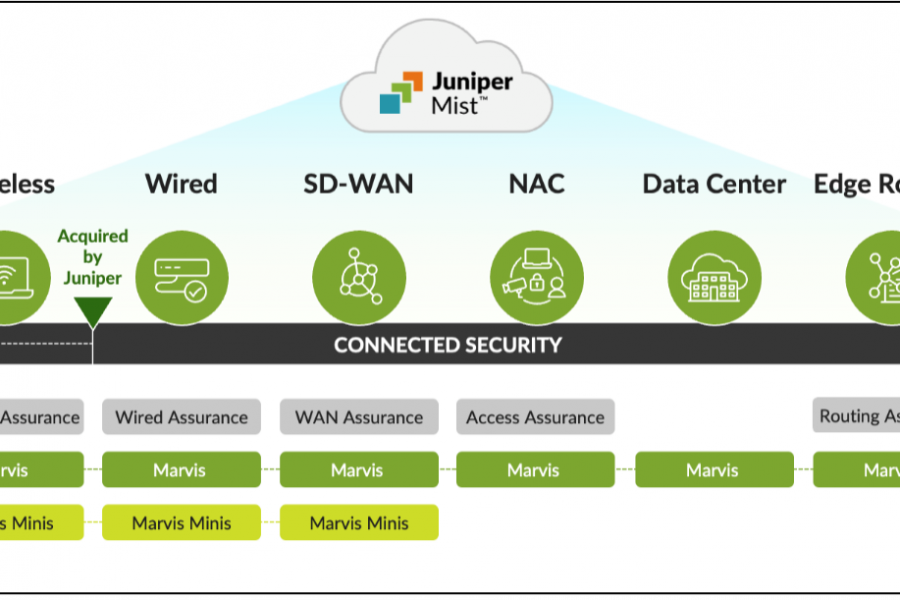
Juniper Connected Security brings today’s most advanced technologies together to help you defend your network. From the endpoint to the edge, and across every cloud in between. See, automate, and protect with Juniper Connected Security.