Quantum key distribution (QKD) is a technology that relies on quantum mechanics to share secret information between two distant locations. To many of us, quantum mechanics are incomprehensible – even Einstein experienced issues grasping quantum mechanics. In response to a letter from German physicist and mathematician Max Born, who was instrumental in the development of quantum mechanics, Einstein said:
Quantum mechanics is very impressive. But an inner voice tells me that it is not yet the real thing. The theory produces a good deal but hardly brings us closer to the secret of the Old One. I am at all events convinced that He does not play dice.
Yet it is precisely the capability of playing dice (a way to generate random numbers) that is the basis for quantum keys and their distribution. QKD exploits two fundamental attributes of quantum mechanics:
- A quantum key in the form of entangled qubits can exist at two places at the same point in time.
- Every attempt to measure a qubit alters the characteristic information of qubits at both places and can immediately be identified. This also implies that a qubit cannot be copied.
So, how does this look in practice?
Quantum Key Distribution Architecture
QKD architectures rely on the internet for non-encrypted communication. Additionally, QKD architectures leverage three communication channels:
- The Crypto Channel: Quantum channels are not well suited to transport anything other than random qubits. To make use of them, quantum keys are shared in an information theoretical safe manner at a rather low bitrate. The keys are subsequently fed into cryptographic algorithms which encrypt massive amounts of data in a separate channel. If the same key is used on both ends of a crypto-channel, the encryption is called “symmetric.” Currently, the most prominent algorithm is AES256, which is considered quantum-safe and used by Ethernet MACsec implementations to encrypt and decrypt flows of 400Gbit/s. MACsec is also a feature implemented in Juniper’s PTX Series routers.
- The Key Exchange Channels: These are the channels by which the devices at the ends of the quantum channel can communicate quantum keys to the devices at the ends of the crypto channel. In other words, this is how quantum keys are exploited.
- The Quantum Channel: Since quantum mechanics describe objects in the physical world, such as photons, devices that deal with quantum keys cannot be virtualized. To maintain the quantum information, qubits need to be communicated by physical transmitters and receivers. In contrast, math-based cryptography (where algorithms can easily be copied to any microprocessor) can easily be distributed via software download. Consequently, deploying QKD requires the presence of dedicated physical equipment.
How would these channels work together to create a secure communication channel?
In Figure 1 below, imagine that Alice wants to set up a call with Bob to exchange confidential information. She decides to use a conference call featuring a highly secure encryption method as a crypto channel. For this service, Alice needs to convey three pieces of information:
- Bob’s email address to convey non-confidential information
- A web link to access the service
- A secret passcode
Since Alice fears that Eve, her adversary, is trying to hack into the connection, Alice doesn’t want to share the passcode over the internet or even rely on the service provider to create one. So, what to do?
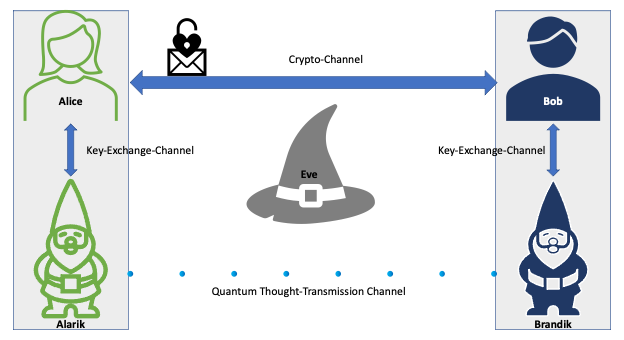
By coincidence, Alice’s neighbor Alarik is a magic gnome, skilled in quantum-thought-transmission. In another astonishing coincidence, Alarik’s twin, Brandik, lives next to Bob.
To say that Alarik and Brandik are a little unusual is an understatement of the first order. They constantly utter magic words to one another, only whispering when doing so. In order to hear them, Alice and Bob must be in close proximity to one another. Additionally, Alarik and Brandik never use the same magic words twice. So, every magic word they say is used only once. If asked to repeat a magic word, Alarik and Brandik can be quite brusque in their dismissal of such nonsensical requests. Alarik and Brandik can also communicate across distances thanks to their magic gnome twin mind connection. They always utter the same unique single-use magic words at the same moment, even though they live far from each other.
Alice realizes that Alarik and Brandik serve as a key exchange channel to keep things secret with Bob. She has the idea to use the magic words of the gnome twins as a passcode for the calls with Bob. So they establish a confidential key exchange channel in a secure location between themselves and their magic gnome twins.
Alice then proposes the following key exchange process to Bob: Alice listens to Alarik, uses his last-uttered magic-word as passcode and creates a call invitation with a link, mailing it to Bob. Since Bob sits next to Brandik, he listens to his last-uttered magic word and uses that as the passcode. Finally, clicking on the link and using his passcode, he will be able to talk to Alice safely and securely.
However, Alice and Bob didn’t think through an important timing issue. Since Alice has no idea when Bob is going to read her email, there is no way to tell if Bob will use the same magic word passcode she uses or a later one. Consequently, the result is usually a mismatch of the passcode used by Alice and Bob.
Then, Alice and Bob convinced their magic gnome neighbors to utter a magic number to correspond to each magic word. Alice randomly selected one of Alarik’s magic words along with the associated magic number. She sent the invite to Bob, adding the magic number to her email. Alice then uses the passcode to set up the call and waits for Bob to dial in. When Bob receives the magic number, he checks his log of Brandik-generated magic words for the corresponding magic number and magic word combination and uses that as passcode for the call with Alice. Voila – success!
What about Eve, Alice’s adversary trying to hack into the communication?
Given that the magic word serving as a key is shared through quantum thought transmission between Alarik and Brandik, the keys can’t be intercepted by Eve. But what about the other communication channels?
Alice and Bob need to be able to exchange unencrypted messages by email to schedule the encrypted call. Consequently, Eve can intercept these messages and can see a number delineating the correct key, but without the magic word key necessary to decrypt the conference call, the email is useless to Eve.
She may then try to masquerade as Bob sending emails to Alice or as Alice when mailing to Bob. To counter such an attack, Alice and Bob know to authenticate their emails with signatures provided by exiting mechanisms like Pretty Good Privacy (PGP). In this way, Alice can rely on the fact that a received email has indeed been authored by Bob and not altered by anyone else. Thus, Eve is foiled again.
Real World Applications of QKD
Yes, this fairytale example is whimsical, but it’s just one example of how quantum-based key exchange actually works. In our universe, where magic gnome neighbors are not the norm, an early installation for a quantum secure industrial network is already operational[1]. Meanwhile, the European Telecommunication Standards Institute (ETSI) aims to simplify quantum applications and published the standard of ETSI GS QKD 014 in February 2019 which specifies the interaction between Quantum Key-Distribution and network devices. In their fairytale world, Alice, Bob, Eve and the gnomes would surely recognize their contributions to the standard.
[1] https://www.forbes.com/sites/johndunn/2020/10/01/bt-is-using-quantum-technology-to-secure-gigabytes-of-sensitive-data-sent-between-two-industrial-sites-in-the-uk/?sh=232bee326ef4